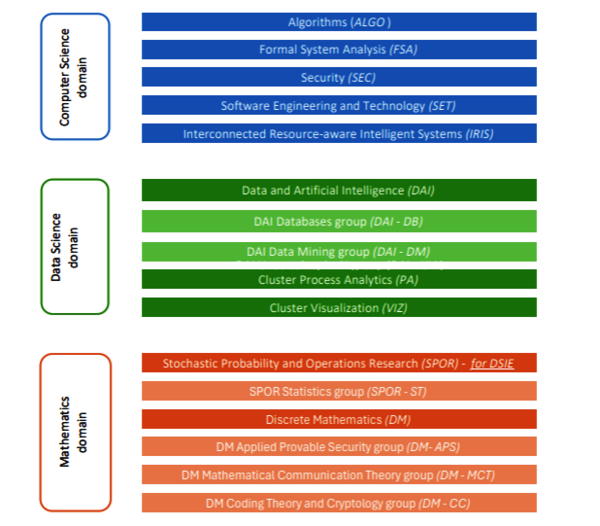
Research groups
As a CSE student you can graduate with one of the research clusters and groups depicted below. On this page you will find more information on these research groups.
Computer Science domain
Cluster ALGO
Website: https://algo.win.tue.nl/
Contact person: prof.dr. Mark de Berg
The ALGO cluster studies the design and analysis of algorithms and data structures, one of the core areas within computer science. Research in ALGO ranges from curiosity-driven to motivated by concrete applications, and from purely theoretical to experimental. In all cases, the goal is to understand the underlying principles of the developed solutions and to formally prove their properties. Our approaches frequently combine the rigorous methods from algorithmic theory – which give performance guarantees with respect to both the quality of solutions and the running time of algorithms – with efficient engineering to achieve results of both theoretical and practical significance.
Within the broad field of algorithms, ALGO specializes in various areas:
- Computational Geometry
- Moving Object Analysis
- Parameterized Complexity
- Geovisualization
- Massive Data
- Mobile Agents
- Networks
- Digital Humanities
- Computational Social Choice
We offer a broad spectrum of possible projects in these areas: very fundamental and theoretical, purely experimental, and combinations of these. We recommend interested students to have a look at our webpage for more details on these topics, as well as an overview of recent theses.
Relevant courses are:
- Advanced Algorithms (2IMA10)
- Geometric Algorithms (2IMA15)
- Algorithms for Geovisualization (2IMA20)
- Massively Parallel Algorithms (2IMA35)
- Exact Algorithms for NP-hard Problems (2IMA25)
- Topological Data Analysis (2IMA30)
- Seminar Algorithms (2IMA00)
- Algorithms for Collective Decision Making (2IMA50)
Other relevant courses:
- Visual Analytics (2AMV10)
- Graphs and Algorithms (2MMD30)
Cluster Formal System Analysis (FSA)
Website: https://fsa.win.tue.nl
Contact person: dr.ir. Tim Willemse (expertise group leader)
The focus of the specialization FSA is on modeling and verifying behavior of systems and programs. Behavior must be understood as all possible actions that a system can perform during its lifetime. The goal is to use this to improve the quality of the software in such systems.
The major techniques that are being used and studied within FSA are process algebraic specification, abstract data types and rewriting, behavioural equivalences, modal logic and model checking, semantics, SAT and SMT solving, program semantics, probabilistic behaviour, streams, active and passive automata learning and proof checkers. Mathematical rigor is an important carrier for all the techniques that we apply.
Our modeling and verification find applications in many fields, varying from source code verification of the software in infrastructure (bridges, trains), heavy industry (Tata steel) to model based design of high-tech equipment (ASML, Philips, Canon). Many of our results, algorithms and methodologies are culminated in the mCRL2 verification toolset, which has become the verification workhorse for many companies and research institutes.
The research that is done in the group covers a wide spectrum. It ranges from finding the appropriate semantics of the combination of non-deterministic and probabilistic behaviour, appropriate syntax and laws for variability analysis of product families, to building automatic software correctness proof engines for PLC code, analysing games, and designing correct software for embedded equipment.
Relevant courses are:
- Automated Reasoning (2IMF25)
- System Validation (2IMF30)
- Algorithms for Model Checking (2IMF35)
- Seminar Formal System Analysis (2IMF00)
- Capita Selecta Formal System Analysis (2IMF05)
- Program Verification Techniques (2IMP10)
- Process Algebra (2IMF10)
- Proving with Computer Assistance (2IMF15)
- Architecture of Distributed Systems (2IMN10)
- Advanced Algorithms (2IMA10)
- Domain Specific Language Design (2IMP20)
Cluster Security (SEC)
Website: https://security1.win.tue.nl/doku.php
Contact person: dr. Boris Skoric
Advanced and nation-state malware, evolving attack engineering techniques evading sophisticated monitoring mechanisms, to the new frontiers of IoT security, access control, and physical security, cybersecurity challenges are countless.
In reaction to this, SEC’s approach to system security is multi-faceted and covers offensive and defensive aspects of system security, trust management and compliance control systems, system monitoring and cyber-physical security, always targeting concrete security problems and addressing the underlying, fundamental issues at their core. SEC’s strength lies precisely in its ability to empirically and theoretically understand the full security process: from attack generation and system management, to policy specification and user aspects.
Research in the Security (SEC) group spans three areas vital to the security of decentralized and embedded systems:
- Security policy specification & enforcement
- Security of embedded systems
- Threat intelligence and defense
SEC sits at the cutting edge intersection of these areas, addressing particularly challenging operative and theoretical problems: for example, by monitoring underground activities and studying the techno-economic principles driving attack production, SEC maintains a unique perspective on the offensive side of computer security. This understanding channels into novel approaches such as new monitoring techniques to detect attacks targeting IT and IoT systems alike and respond to these with adaptive security and authentication mechanisms.
SEC has made significant contributions to secure key storage in embedded systems by devising algorithms for randomness extraction from Physical Unclonable Functions (PUFs).
Relevant courses are:
- Seminar Information Security Technology (2IMS00)
- Verification of Security Protocols (2IMS15)
- Principles of Data Protection (2IMS25)
- Cyberattacks Crime and Defenses (2IMS20)
- Cryptology (2MMC10)
- Cryptographic Protocols (2DMI00)
- Applied Cryptography (2DMI10)
- Physical Aspects of Digital Security (2IMS10)
- Advanced Network Security (2IMS30)
- Software security (2DMI20)
- Intrusion Detection Laboratory (2IMS40)
- Introduction to Quantum Computing and Security (2IMS50)
- Software Security (2DMI20)
- Applied Cryptography (2DMI10)
- Intrusion Detection Laboratory (2IMS40)
Cluster Software Engineering and Technology (SET)
Website: https://research.tue.nl/en/organisations/software-engineering-and-technology-w
Contact person: dr.ing. Anton Wijs
Software has become one of the key enablers of modern society. In almost all activities that we do as human beings software plays a role, whether this is using social media, buying goods, monitoring our sports activities, or in the production of goods.
The high-tech industry, in particular, is facing two trends. First of all, the amount of software is growing rapidly. Secondly, the quality of software is decreasing. These trends result in new research challenges. How to develop more high-quality software in less time? How to guarantee the quality of the software? How to deal with the huge amount of existing software? The answers to these questions are not straightforward. Common themes in answering these questions are software architecture, model driven software engineering (MDSE), software verification, and software evolution.
Software architecture captures the high-level organisation of a system and represents this through multiple complementary views (including structure and behaviour). The design of the architecture determines many of the quality properties of a system, such as cost, performance, reliability and maintainability. Some of the key questions in architecting are: i) to balance the many quality objectives, and ii) to ensure that the architecture and implementation are kept consistent with each other while the system evolves.
Models provide a higher level of abstraction and thus allow the specification of more functionality in less code. The models can also be used as a starting point for simulation and verification. Finally, existing software can be analysed and the underlying models can be extracted. The research focus of the research group SET is on model based software development and on software evolution. The field of model based software development is broad. One key research area is the development of tooling to support the development of models in domain specific formalisms using meta-modeling techniques. Research on tooling for model based software development includes the modularity of meta-models, the description of semantics of domain specific languages, the verification of model transformation formalisms, the co-evolution of models and meta-models, and the correct generation of code. The ultimate goal is to create a tool set which provides high fidelity software generation. Our research in MDSE also includes the management and consistency checking of models, especially in the context of high-tech systems, where variability and the use of digital twins are two important aspects we consider.
Another key research area is empirical studies - i.e. the study of software- development and - evolution by observing projects in practice (either open source or in companies).
Software verification and correctness-by-construction address the functional correctness of software. Techniques such as model checking and program verification can be applied to prove correctness of both models and (generated) code, but also of model transformations. Particular attention is paid to the usability of those techniques, both regarding their performance and their required expert-level. High-performance, easy to use techniques are most suitable to be adopted in MDSE workflows. To this end, research is being done to automate the verification process as much as possible, and to accelerate the involved computations (model checking, SAT solving) by means of multithreading and the use of graphics processors. In correctness-by-construction, research is being done to scale the approach, in particular to families of related programs.
Software evolution encompasses the entire life cycle of a software system, from inception to phase out. As a research domain, software evolution aims at obtaining insights in how and why software evolves as well as at translating those insights into techniques for assessing system evolvability and facilitating evolution. Software evolution is an activity carried out by humans. Therefore, in addition to technical aspects, such as inter-system dependencies and source code vulnerabilities research in software evolution also considers social (e.g., team diversity, mentoring, emotion in developer communication) and socio-technical ones (e.g., social debt and technical debt). Similarly to studies of models, the lion’s share of software evolution research is empirical in nature.
Relevant courses are:
- Program Verification Techniques (2IMP10)
- Software Project Management (2IMP15)
- Domain Specific Language Design (2IMP20)
- Software Evolution (2IMP25)
- System Design Engineering (2IMP30)
- Empirical Methods in Software Engineering (2IMP40)
- Seminar Software Engineering and Technology (2IMP00)
- Capita Selecta Software Engineering and Technology (2IMP05)
- Human-Computer Interaction (2IMP60)
Other relevant courses:
- Foundations of Data Mining (2AMM20)
- Advanced Process Mining (2AMI20)
- Architecture of Distributed Systems (2IMN10)
Cluster Interconnected Resource-aware Intelligent Systems (IRIS)
Website: https://iris.win.tue.nl
Contact person: prof. dr. Nirvana Meratnia
Science and technology have changed the way we live, communicate, work, and even spend our free time. We are surrounded by systems of varying sizes and forms that sense, communicate, and try to make sense of what happens, with, within, and around us or where they operate (e.g. in a car or at a factory). The goal of all these systems is to create a safer, healthier, more pleasant, and more productive environment. As the scale, complexity, heterogeneity, and extent of usage of these systems increase, so do the performance challenges of these systems.
IRIS focuses on design, analyze, develop, and evaluate concepts, models, algorithms, protocols, and tools that optimize (distributed embedded) systems performance in terms of timing behavior, dependability, programmability, reliability, robustness, scalability, accuracy, energy and data computation efficiency, and trustworthiness. This is done within three research pillars, i.e., Pervasive networking (covering edge networking, (IoT) communication and interoperability, (IoT) network resource management), Pervasive computing (covering edge computing and federated learning, edge-driven data analytics and machine learning, embedded AI, and explainable AI), and Predictable performance (covering time-sensitive networks, realtime distributed systems, resource management and scheduling, formal modeling, analysis & verification, and model-based engineering of cyber physical systems).
Relevant courses are:
- Real-Time Systems (2IMN20)
- Quantitative Evaluation of ES (2IMN25)
- Architecture of Distributed Systems (2IMN10)
- Internet of Things (2IMN15)
- Machine Learning for Industry (2IMN30)
- Seminar Interconnected Resource-aware Intelligent Systems (2IMN00)
Other relevant courses:
- Algorithms for Model Checking (2IMF35)
- System Validation (2IMF30)
- Deep Learning (2AMM10)
- Machine Learning Engineering (2AMM15)
- Text Mining (2AMM30)
- Uncertainty Representations and Reasoning (2AMU30)
Data Science domain
Cluster Data and Artificial Intelligence (DAI) - Databases (DB)
Website: https://dai.win.tue.nl
Contact person: prof.dr. George Fletcher
Data-intensive systems are crucial in modern computing, analytics, and data science. The Database (DB) group studies core engineering and foundational challenges in scalable and effective management of big data. Current research in the DB group focuses primarily on problems in streaming data, data approximation, the interaction of programming and query languages, and the management of massive graphs such as social networks, financial networks, and biological networks. Expertise within the group includes query language design and foundations, query optimization and evaluation, data analytics, data integration, and database education. In addition to dissemination of research results in the leading scientific venues in the data management field, the DB group impacts the broader community through open-source software development, training and mentoring of early-career scientists, industrial R & D collaborations, and serving on international efforts such as the LDBC Graph Query Language Standardization Task Force.
DB group investigations into both the theory and engineering of data management systems are inspired by real-world application scenarios in close cooperation with public-sector and industrial research partners. Academic partners of the group range across leading research groups in Europe, Asia, and North America. Recent collaborators include Oracle Labs, Neo4j, University of Toronto, National University of Singapore, University of Lyon 1, and TU Dresden.
Relevant courses are:
- Seminar Datamanagement (2IMD00)
- Capita Selecta Databases (2IMD05)
- Big Data Management (2AMD15)
- Engineering Data Systems (2IMD10)
- Knowledge Engineering (2AMD20)
Cluster Data and Artificial Intelligence (DAI) - Data Mining (DM)
Website: https://dai.win.tue.nl
Contact person: prof.dr. Mykola Pechenizkiy
Datamining and information retrieval automate the extraction of information and knowledge from large amounts of data; often so much data is collected that manual analysis is no longer possible.
Data mining and information retrieval assist data analysts in locating relevant information and patterns in the data.
Relevant courses are:
- Machine Learning Engineering (2AMM15)
- Research Topics in Data Mining (2AMM20)
- Deep Learning (2AMM10)
- Seminar Data Mining (2IMM00)
- Capita selecta Data Mining (2IMM05)
Cluster Data and Artificial Intelligence (DAI) - Uncertainty in AI (UAI)
Website: https://dai.win.tue.nl
Contact person: prof.dr. Cassio de Campos
The group explores uncertainty in AI and machine learning from multiple angles on principles of AI, theories of representation, probabilistic AI models, algorithms for learning, reasoning and decision making. We are greatly interested in probabilistic graphical models, generative models and causality. There is also an important focus on approaches that are not only accurate but efficient, interpretative, robust and fair.
Relevant courses are:
- Generative AI Models (2AMU20)
- Foundations of Artificial Intelligence (2AMU10)
- Uncertainty representation and reasoning (2AMU30)
- Seminar Uncertainty in AI (2IMU00)
- Capita Selecta Uncertainty in AI (2IMU05)
Cluster Process Analytics (PA)
Website: https://pa.win.tue.nl
Contact person(s): See link above. For signing the study program contact the Secretary IS.
The Process Analytics (PA) research group investigates methods, techniques and tools for the design and analysis of Process-Aware Information Systems (PAIS), i.e., systems that support business processes (workflows) inside and between organizations.
PA is not only interested in these information systems and their architecture, but also model and analyze the business processes and organizations they support. The group aims at results that are highly original and applicable in real-life situations. The main three research lines of AIS are:
- Process Modeling and Analysis. Models are commonly used to answer questions related to correctness and performance. One of the main goals here is to further improve verification techniques to check various properties such as soundness, data/resource soundness, accordance, controllability, and selected temporal properties. Pattern-based approaches are used for correctness-by-design. Another goal is to develop innovative simulation approaches that better reflect reality and that can be used in an operational setting while using process mining results.
- Process Mining. Process mining techniques are used to extract process-related information from event logs, e.g., to automatically discover models, check conformance, and augment existing models with additional insights extracted from some event log. The goals are to significantly improve the state-of-the-art in process discovery, to advance the state-of-the-art in conformance checking, and to predict problems, i.e., pro- vide warnings based on historic information (e.g., a case will be late or an error is likely to occur).
- PAIS Technology. PAISs are used to manage and execute operational processes involving people, applications, and/or information sources. Examples are WFM (Workflow Management), BPM (Business Process Management), and ERP (Enterprise Resource Planning) systems. Increasingly, these systems are driven by models and produce high-quality event logs. We are interested in the artifacts used and produced by these systems (i.e., models and logs) as these are essential for testing the techniques developed in the two other research lines. For example, it is interesting to convert and verify process models expressed in some particular industry language. The same holds of course for event logs. Service-orientation plays an important role here and this new architectural style poses new research questions.
Relevant courses are:
- Foundations of Process Mining (2AMI10)
- Advanced Process Mining (2AMI20)
- Seminar Process Analytics (2IMI00)
- Capita selecta Process Analytics (2IMI05)
Cluster Visualization (VIZ)
Website: https://vis.win.tue.nl
Contact person: prof. dr. Anna Vilanova
Contact person Master projects: dr.ir. Huub van de Wetering
Data visualization aims to provide insight in large data sets by using interactive graphics, exploiting the unique capabilities of the human visual system to detect patterns and structures.
By presenting data visually, people can see unexpected relations; by offering interaction they are enabled to explore huge data sets, driven by their interest.
The Visualization cluster focuses on the development of new methods and techniques to explore and present large data sets. The focus is on data visualization and visual analytics. We study how to provide insight in large, heterogeneous data sets, such as combinations of multivariate data, high dimensional data, complex imaging data, network data, event data, and geospatial data, all often time varying. We study how to incorporate methods from statistics and AI to support human analysis, understanding, and decision making. Visual analytics for AI can provide more effective and efficient model development, and more trust and confidence on AI based decisions.
We develop novel approaches that go from fundamental research to application oriented visual designs. We cooperate with experts from a variety of application domains, including health care, machine learning, bioinformatics, forensics, and fraud detection; both from academia and industry (e.g., Philips).
Another interest is in high performance scientific computing: exploiting the power of GPUs for visualization and computer graphics, with physically based animation and 3D shape analysis as typical applications.
Furthermore, in cooperation with the Centrum voor Wiskunde en Informatica (CWI) virtual reality systems are studied. Typical topics include the design and evaluation of 3D interactive techniques and methods for improving image quality in virtual reality displays.
Relevant courses for the VIS specialization are:
- Visual Analytics (2AMV10)
- Geometric algorithms (2IMA15)
- Visual computing project (2IMV10)
- Simulation in computer graphics (2IMV15)
- Interactive virtual environments (2IMV25)
- Seminar visualization (2IMV00)
- Capita selecta visualization (2IMV05)
Other relevant courses:
- Machine Learning Engineering (2AMM15)
Mathematics Domain
Cluster Stochastic Probability and Operations Research (SPOR)
!! Please note this group is a graduation option for DSiE students only !!
Research group: Statistics
Website: https://www.tue.nl/en/research/research-groups/mathematics/statistics-probability-and-operations-research
Contact person: dr. Fiona Sloothaak
At a high level, we study the underlying mathematical structure of complex systems, and develop effective techniques to analyze and optimize them. All such systems arise and are inspired by real-world applications. Therefore, we investigate them from a double perspective: we aim at advancing their theoretical foundations, while at the same time maintaining strong ties and connections with industry and other scientific domains.
Likewise, the education portfolio revolves around rigorous mathematical concepts and stylized models, but with an eye towards real-life problems and applications.
Statistics group develops and compares data-analytical methods for analyzing and sampling complex structured correlated data sets. It includes parameter estimation, model fitting, latent variable models, mixed models, missing data, statistical process control, survival and reliability theory, time series analysis, and statistical learning methods. One of the central themes is the analysis of high-dimensional temporal data sets and other large data sets. Applications include data science and machine learning, biopharmaceutical companies, chemical industry, medical centers.
Relevant courses are:
- Longitudinal Data Analysis (2AMS10)
- Statistics for big data (2AMS20)
- Statistical Learning Theory (2DI70)
- Time-Series analysis & forecasting (2DD23)
Cluster Discrete Mathematics - Applied Provable Security (APS)
Website: https://www.tue.nl/en/research/research-groups/applied-and-provable-security
Contact person: dr. Andreas Hülsing
The Applied and Provable Security (APS) group does research in the application of cryptography as well as formally arguing about the security of cryptographic solutions. The most basic cryptographic systems are aimed at ensuring the secrecy and authenticity of a message. However, in practice we are interested in the security of more complex protocols like those used to secure Internet connections or used in messaging applications. APS does research in how to design secure basic cryptographic systems and how to construct secure protocols from these.
The APS team has a special focus on security in the presence of attackers with access to a quantum computer, so called post-quantum cryptography. Research in APS has links to many other domains in M&CS, including algorithms, complexity theory, (quantum) information theory, formal methods, and of course the general security area.
The group is part of the Department of Mathematics and Computer Science within the section Discrete Mathematics.
Cluster Discrete Mathematics - Mathematical Communication Theory (MCT)
Website: https://www.tue.nl/en/research/research-groups/mathematics/discrete-mathematics/mathematical-communication-theory
Contact person: dr. Alberto Ravagnani
Data communication is about reliably communicating over a possibly noisy channel, efficiently storing and retrieving data, and guaranteeing their integrity. The MCT group focuses on various research directions at the crossroad of communication theory and applied discrete mathematics:
- error-correcting codes (coding theory) in various metrics;
- optimization for data storage and recovery;
- network coding;
- quantum error correction;
- enumerative and algebraic combinatorics; and
- code-based (post-quantum) cryptography.
The group is part of the Department of Mathematics and Computer Science within the section Discrete Mathematics.
Cluster Discrete Mathematics - Coding Theory and Cryptology (CC)
Website: https://www.tue.nl/en/research/research-groups/mathematics/discrete-mathematics/coding-theory-and-cryptology
Contact Person: prof dr T. Lange
Coding Theory is the mathematical theory of encoding information in such a way that it becomes resistant to transmission errors. The main topics are the study of the properties of various codes (cyclic codes, BCH-codes, MDS-codes, algebraic-geometric codes) and the construction of efficient decoding algorithms for these codes.
Cryptology is the mathematical theory of protecting information against unauthorized access (privacy), determining if a message has been altered by a third party (integrity), adding a signature to an electronic document and verifying the identity.
The group is part of the Department of Mathematics and Computer Science within the section Discrete Mathematics.